Security-First Architecture
Security isn't a feature you add after launch. It's an architectural property — either the system was designed for it, or it wasn't.

When You Need This
You're operating in a regulated industry where a data breach means fines, lawsuits, and loss of customer trust — not just a PR incident. Or you're building enterprise software where security questionnaires, SOC 2 audits, and penetration test reports are prerequisites for closing deals. You need an architecture where security is structural — zero trust networking, encryption at every layer, least-privilege access, comprehensive audit trails, and automated compliance checks — not a checklist applied after the system is built.
Pattern Overview
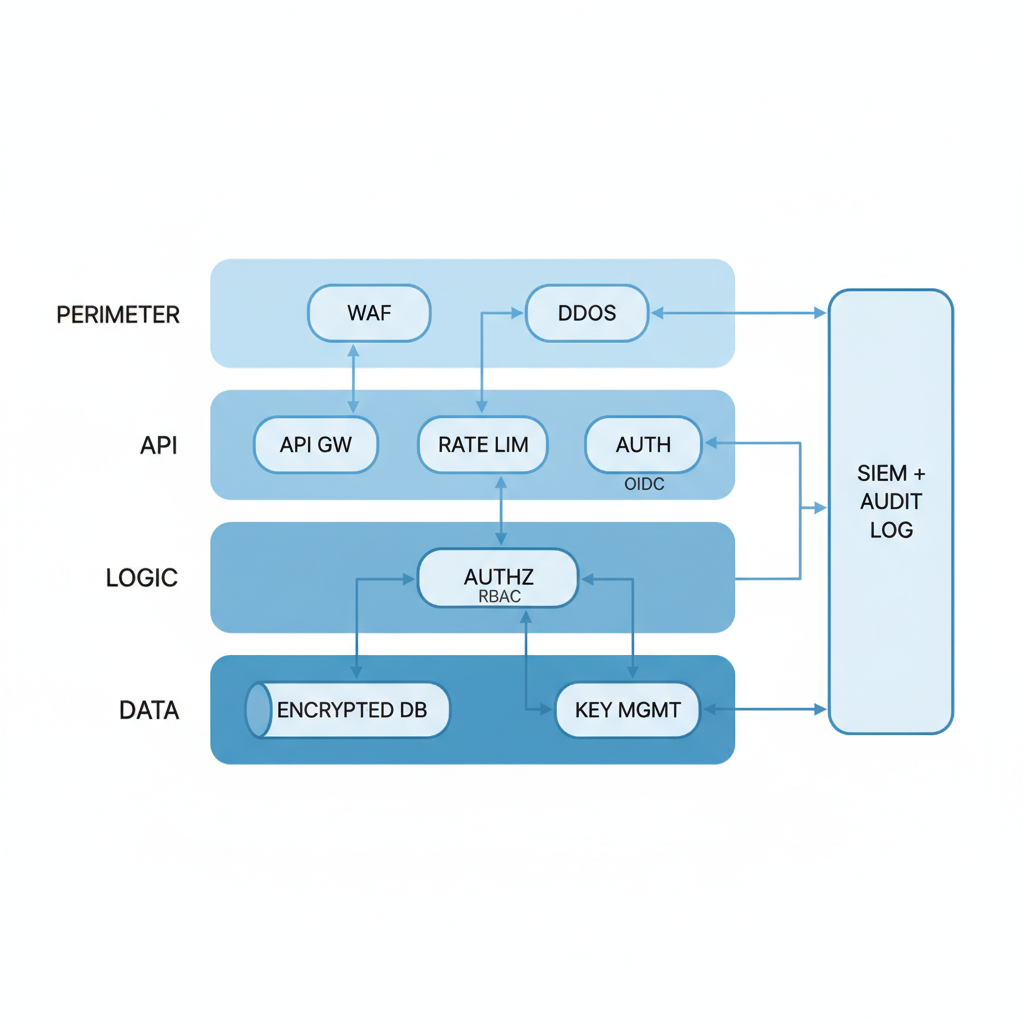
Security-first architecture embeds security controls at every layer of the system: network (zero trust, micro-segmentation), identity (centralized IAM, MFA, short-lived tokens), data (encryption at rest and in transit, field-level encryption, key rotation), application (input validation, OWASP protections, dependency scanning), and operational (audit logging, SIEM integration, incident response automation). The architecture assumes breach — it's designed to limit blast radius, detect compromise quickly, and maintain audit trails that support forensic investigation.
Reference Architecture
The architecture implements defense in depth across five layers. Network layer: zero trust with mutual TLS between services, no implicit trust based on network location. Identity layer: centralized identity provider (Okta, Auth0, Clerk) with MFA, RBAC/ABAC policies, and short-lived tokens (15-minute JWTs, not session cookies). Data layer: envelope encryption with AWS KMS or Vault, field-level encryption for PII, and data classification tags. Application layer: WAF, input validation, CSRF/XSS protection, rate limiting, and dependency vulnerability scanning. Operations layer: centralized audit logging, SIEM correlation, automated compliance checks, and incident response playbooks.
- Identity & Access Management: Centralized IdP (Okta, Auth0, Clerk) with SSO, MFA, and SCIM provisioning. RBAC for coarse-grained permissions, ABAC for fine-grained (e.g., "can access records in own department"). Service-to-service authentication via mTLS or signed JWTs — no shared API keys between services
- Encryption Engine: Envelope encryption — data is encrypted with a data encryption key (DEK), the DEK is encrypted with a master key (KEK) in AWS KMS or HashiCorp Vault. Key rotation on schedule (90 days) without re-encrypting existing data. Field-level encryption for sensitive columns (SSN, credit card, health data) with application-level decrypt
- Audit & Compliance Pipeline: Every state change, access attempt, and administrative action is logged to an append-only audit store (immutable S3, CloudTrail, or custom audit service). Logs are structured (JSON), searchable, and retained per compliance requirements (7 years for financial, 6 years for HIPAA). Automated compliance checks run daily against CIS benchmarks and flag drift
- Threat Detection & Response: WAF (AWS WAF, Cloudflare, Vercel Firewall) at the edge for OWASP Top 10 protection. SIEM (Datadog Security, Splunk, Elastic Security) correlates events across services to detect anomalous patterns. Automated incident response: suspicious login triggers account lockout, data exfiltration pattern triggers network isolation
Design Decisions & Trade-offs
System Architecture Overview
Technology Choices
| Layer | Technologies |
|---|---|
| Identity | Okta, Auth0, Clerk, AWS IAM, HashiCorp Vault (secrets) |
| Network | Istio mTLS, AWS PrivateLink, VPC peering, Vercel Firewall, Cloudflare WAF |
| Encryption | AWS KMS, HashiCorp Vault, application-level (NaCl/libsodium) |
| Audit | CloudTrail, Datadog Audit, custom audit service (append-only S3 + Athena) |
| SIEM | Datadog Security, Splunk, Elastic Security, AWS Security Hub |
| Compliance | Prowler, ScoutSuite, Snyk, Trivy, OPA/Rego, Vanta (SOC 2 automation) |
When to Use / When to Avoid
| Use When | Avoid When |
|---|---|
| Regulated industry: financial services, healthcare (HIPAA), government (FedRAMP) | Internal tool with no sensitive data and no compliance requirements |
| Enterprise deals require SOC 2, ISO 27001, or HIPAA compliance | You're building an MVP where security basics (HTTPS, auth, input validation) suffice |
| The system processes PII, financial data, or health records | Over-engineering security adds months to delivery with no compliance mandate |
| Breach would cause significant financial or reputational damage | The cost of security controls exceeds the cost of a potential breach (risk assessment) |
Our Approach
MW embeds security into the development lifecycle, not as a gate at the end. Our infrastructure templates include encryption, audit logging, and IAM policies by default — teams opt out of security controls (with justification), not opt in. We run automated OWASP ZAP scans in CI, dependency vulnerability checks on every PR, and infrastructure compliance checks on every Terraform apply. For compliance-heavy engagements, we deliver a "compliance package" alongside the system: SOC 2 evidence collection automation, audit log retention policies, incident response runbooks, and penetration test-ready documentation.
Related Blueprints
- AI-Powered Security Operations Center — AI-driven threat detection and automated incident response
- GDPR Compliance Data Platform — Data mapping, consent management, and right-to-erasure automation
- Zero Trust Network Architecture — Full zero trust implementation with micro-segmentation
- Automated Penetration Testing Platform — Continuous automated security testing
- Healthcare HIPAA Compliance System — HIPAA-specific controls for healthcare platforms
Related Case Studies
- Contextual Encryption — Application-level field encryption with context-aware key management
- Okta SSO/SCIM Integration — Enterprise authentication with SSO and automated user provisioning
- GDPR-Compliant AI Chat — Multi-model chat platform with GDPR data handling and retention controls
Related Architecture Patterns
Explore more design patterns and system architectures

Serverless-First Architecture
Pay for what you use, scale to zero when you don't, and stop managing servers entirely — but know when the economics stop working.

On-Off Scaling Architecture
Don't pay for idle GPUs. Provision compute just-in-time, process the workload, and tear it down — turning capital expense into a per-job operating cost.

Edge Computing & IoT Architecture
Process data where it's generated. Not everything needs to round-trip to the cloud — and for many IoT workloads, it can't.
Need Help Implementing This Architecture?
Our architects can help design and build systems using this pattern for your specific requirements.
Get In Touch